Enter the Era of Agentic Security
Built for regulated enterprises, financial institutions, government environments, and SMBs with serious security and compliance needs.
Connect Your Stack in Minutes. Make it Agentic.
Built for regulated enterprises, financial institutions, government environments, and SMBs with serious security and compliance needs.
Connect Your Stack in Minutes. Make it Agentic.
Attackers operate at machine speed.
Defenders operate at human speed.
That gap isn’t a skills problem it’s a design problem.
When adversaries compress breach-to-exfiltration time to minutes, SOC teams averaging four-hour response windows face an unwinnable equation.
The future isn’t better detection. It’s autonomous prevention.
Kent Noyes, Global Head of AI & Cyber Innovation at Cisco
Jon Miller, CEO at Halcyon
Natalia Oropeza, Chief Cybersecurity Officer at Siemens
Elia Zaitsev, CTO at CrowdStrike
Haider Pasha, Chief Security Officer EMEA & LATAM at Palo Alto Networks
Darktrace Security Research Team at Darktrace
CISA Official Statement at CISA
Haider Pasha, Chief Security Officer EMEA & LATAM at Palo Alto Networks
Elia Zaitsev, CTO at CrowdStrike
Christopher Wray, FBI Director at FBI
Palo Alto Networks Security Operations Report 2025 at Palo Alto Networks
The Principles Behind Our Autonomous Defense
Automated threats operate at machine pace. Our agents respond at the same velocity 24/7, zero human delay.
Intruders breach in minutes, expand for days. We isolate threats in real time .
Identity, endpoint, cloud breaches span all three. One intelligence layer monitors every domain.
Static defenses become obsolete. We learn from every incident to stop tomorrow’s techniques .
AI agents continuously detecting misconfigurations, remediating threats, and maintaining compliance across AWS, Azure, and GCP in real time.
AI agents continuously monitor, assess, and enforce security across your entire cloud estate closing exposure gaps before attackers find them.
Overall cloud security score and critical findings.
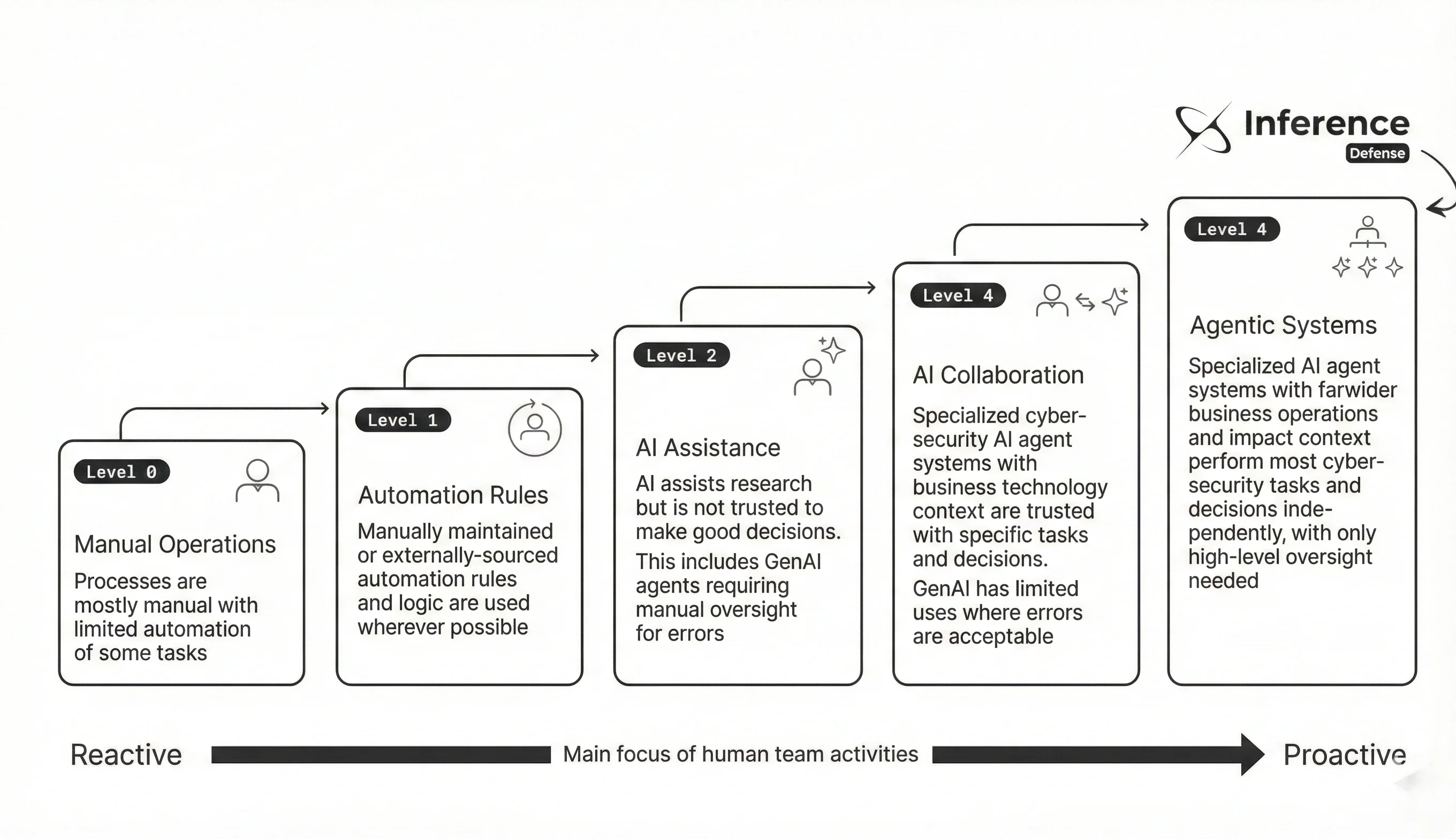
We apply an agentic approach that achieves total operational superiority over adversaries agents handle detection and response continuously while humans provide oversight and manage exceptions.
/var/log/adr-platform.log
We built an agentic, persistent adversary working for you finding exploitable weaknesses before real attackers can.
6*7A0^!HIETD@6XS749%2$4L4RO$SH*8W#6OPLLF%WSKVI^PTT1PJUOS60EQL$*K53*Y#AK5GDM6XIWX79XR^DQOMEJF$F1ZNL*L0Z&#LJ4B$E97Q76VF0U#HY!37J5$GKCI0RMK$2P1F9JJYGVR@IAHYPZALXQMJ!519!GZTQSA$#BEXUYPSZ302Z*&DDWW!NI61S#!MAHJ0Y&3J8*EBIMM$#X%46NJ0*9P3L@UW5A8NCZX&98CQ75NL9XEH11NBB^E&LQ1YPZALMJ3DSUXBS9*DADQ7ND0SCI#HY!37J5$GKKAUGDYE@#8CBDUFA9#3EYGVR@IAHZCUKIYPZALX#3EYZX&98CQ75NL9XJ4B$E97Q76VF0LKU8S5KVSD9$#BEX2Z9HSABIU#CSDK@SN!
Liam Parker
AI agents attempt to breach your environment 24/7, chaining exploits the way real attackers do from initial access to critical asset compromise.
No theoretical risks. We test actual attack chains: stolen credentials → lateral movement → privilege escalation → data exfiltration.
Get exploitable paths ranked by severity and business impact, not a 200-page report. Fix what matters, validate the fix immediately.
Critical vulnerabilities detected
Blocked 2m ago
Blocked 5m ago
Blocked 8m ago
We built an agentic compliance engine working for you delivering audit-ready evidence instantly instead of weeks of manual documentation.
Enterprise-grade security solutions tailored to your needs.
Ransomware Prevention
Detection & Response
Cloud Compliance
Identity Governance

An in-depth analysis of how prompt injection attacks target autonomous AI agents, exploit tool-calling pipelines, and bypass safety guardrails in multi-step agentic workflows.
By
Research Team
Published
Apr 8, 2026

A comprehensive study of zero-day vulnerabilities targeting cloud-native infrastructure — from container escapes to serverless function abuse and misconfigured IAM privilege chains.
By
Research Team
Published
Feb 14, 2026

Investigating adversarial techniques used to poison training pipelines, backdoor open-source model weights, and compromise AI model registries in enterprise deployments.
By
Research Team
Published
Jan 20, 2026
Built to keep you ahead of emerging threats. Completely free.